Operation Trust
An informational article presenting evidence that Q is a modern day version of Operation Trust
Disclaimer & Open Dialog
I am more than happy to have a productive conversation with anyone who has fair evidence against this post. I am here to learn and I am not here to argue or fight or pick sides. I care about the truth first and foremost. If anybody out there has evidence that’s credible that anyone within the Q Movement is indeed doing something to help survivors or to help bust human traffickers please help me understand. I would love to see some evidence that this is actually real and there is work being done to bust child traffickers. That being said, please only use CREDIBLE EVIDENCE, this is important if we’re going to have an effective dialog. I am happy to speak to anyone who’s willing to talk to me in a rational manner.
Operation Trust
New Lies For Old pp. 13, 14
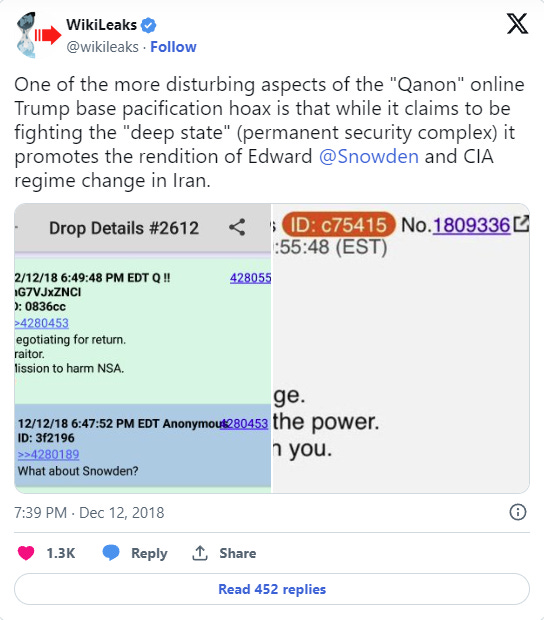
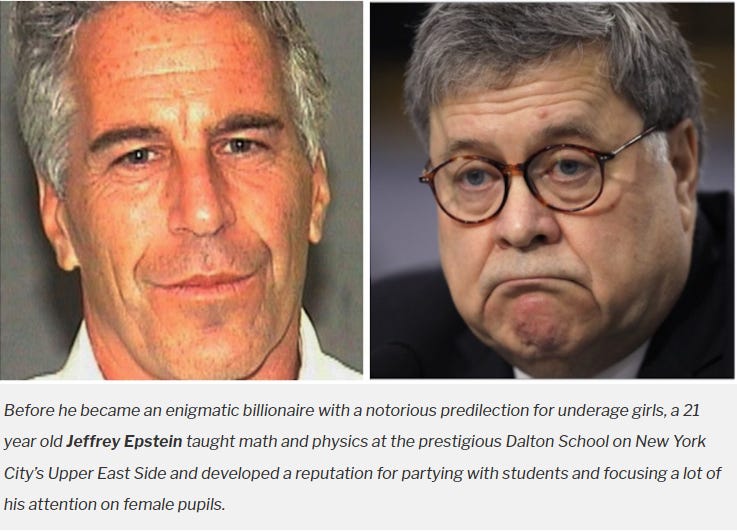
Q-Anon made Trump supporters who were right to be angry over the criminal nature of our ruling class delude themselves with fantasies that “White hats” in the military were going to save us while Attorney General William Barr was busy covering-up the Jeffrey Epstein case and the Kushner administration was busy pardoning fraudsters who donated to the Aleph Institute and releasing traitor Jonathan Pollard from parole to “make aliyah” in Israel.
That sounds like the Confucius-style nonsense put out by Q-Anon.
(Source: https://historyheist.com/glossary/operation-trust/)
(Source: https://x.com/wikileaks/status/1073014563187163136)
(Source: https://x.com/wikileaks/status/1011273751143550979)
(Source: https://www.informationliberation.com/?id=61954)
(Source: https://lawandcrime.com/high-profile/the-epstein-barr-problem-of-new-york-citys-dalton-school/)
Wikipedia’s Article on Operation Trust
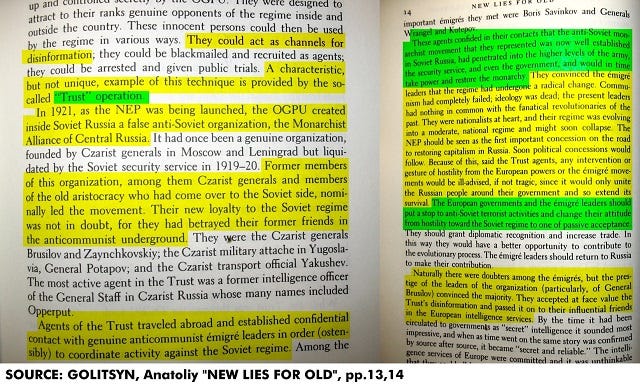
Operation Trust was a counterintelligence operation of the State Political Directorate (GPU) of the Soviet Union. The operation, which was set up by GPU's predecessor Cheka, ran from 1921 to 1926, set up a fake anti-Bolshevik resistance organization, "Monarchist Union of Central Russia", MUCR, in order to help the OGPU identify real monarchists and anti-Bolsheviks. The created front company was called the Moscow Municipal Credit Association.
[...] The one Western historian who had limited access to the Trust files, John Costello, reported that they comprised thirty-seven volumes and were such a bewildering welter of double-agents, changed code names, and interlocking deception operations with "the complexity of a symphonic score", that Russian historians from the Intelligence Service had difficulty separating fact from fantasy.
Wikipedia Article on Operation Trust
Jan 6th Cleaning House of Q Supporters
Just as opposition were outed and arrested by Operation Trust, potentially dozens of Q-Anoners were outed and arrested as a result of the march on the Capitol.
(Source: https://x.com/kylegriffin1/status/1349863868898697216)
Johnathan Pollard
Jonathan Pollard, a US-born Jewish-American intelligence analyst who stole US military secrets and sold them to Israel, received a hero's welcome on Wednesday by Prime Minister Benjamin Netanyahu after being flown out of the US on billionaire GOP megadonor Sheldon Adelson's personal private plane.
Pollard had the terms of his parole quietly lifted by the Trump administration last month to allow him to make aliyah ("ascend"/emigrate to) in Israel.
(Source: https://www.informationliberation.com/?id=61973)
(Source: https://x.com/infolibnews/status/1347386141461381120)
Cass R. Sunstein’s Paper on Conspiracy Theories
Free Copy of the Paper
Many millions of people hold conspiracy theories; they believe that powerful people have worked together in order to withhold the truth about some important practice or some terrible event. A recent example is the belief, widespread in some parts of the world, that the attacks of 9/11 were carried out not by Al Qaeda, but by Israel or the United States. Those who subscribe to conspiracy theories may create serious risks, including risks of violence, and the existence of such theories raises significant challenges for policy and law. The first challenge is to understand the mechanisms by which conspiracy theories prosper; the second challenge is to understand how such theories might be undermined. Such theories typically spread as a result of identifiable cognitive blunders, operating in conjunction with informational and reputational influences. A distinctive feature of conspiracy theories is their self-sealing quality. Conspiracy theorists are not likely to be persuaded by an attempt to dispel their theories; they may even characterize that very attempt as further proof of the conspiracy. Because those who hold conspiracy theories typically suffer from a “crippled epistemology,” in accordance with which it is rational to hold such theories, the best response consists in cognitive infiltration of extremist groups. Various policy dilemmas, such as the question whether it is better for government to rebut conspiracy theories or to ignore them, are explored in this light.
Conspiracy Theories, Cass Sunstein, page 2
Cognitive Infiltration
Rather than taking the continued existence of the hard core as a constraint, and addressing itself solely to the third-party mass audience, government might undertake (legal) tactics for breaking up the tight cognitive clusters of extremist theories, arguments and rhetoric that are produced by the hard core and reinforce it in turn. One promising tactic is cognitive infiltration of extremist groups. By this we do not mean 1960s-style infiltration with a view to surveillance and collecting information, possibly for use in future prosecutions. Rather, we mean that government efforts might succeed in weakening or even breaking up the ideological and epistemological complexes that constitute these networks and groups.
How might this tactic work? Recall that extremist networks and groups, including the groups that purvey conspiracy theories, typically suffer from a kind of crippled epistemology. Hearing only conspiratorial accounts of government behavior, their members become ever more prone to believe and generate such accounts. Informational and reputational cascades, group polarization, and selection effects suggest that the generation of ever-more-extreme views within these groups can be dampened or reversed by the introduction of cognitive diversity. We suggest a role for government efforts, and agents, in introducing such diversity. Government agents (and their allies) might enter chat rooms, online social networks, or even real-space groups and attempt to undermine percolating conspiracy theories by raising doubts about their factual premises, causal logic or implications for political action.
In one variant, government agents would openly proclaim, or at least make no effort to conceal, their institutional affiliations. A recent newspaper story recounts that Arabic-speaking Muslim officials from the State Department have participated in dialogues at radical Islamist chat rooms and websites in order to ventilate arguments not usually heard among the groups that cluster around those sites, with some success. In another variant, government officials would participate anonymously or even with false identities. Each approach has distinct costs and benefits; the second is riskier but potentially brings higher returns. In the former case, where government officials participate openly as such, hard-core members of the relevant networks, communities and conspiracy-minded organizations may entirely discount what the officials say, right from the beginning. The risk with tactics of anonymous participation, conversely, is that if the tactic becomes known, any true member of the relevant groups who raises doubts may be suspected of government connections. Despite these difficulties, the two forms of cognitive infiltration offer different risk-reward mixes and are both potentially useful instruments.
There is a similar tradeoff along another dimension: whether the infiltration should occur in the real world, through physical penetration of conspiracist groups by undercover agents, or instead should occur strictly in cyberspace. The latter is safer, but potentially less productive. The former will sometimes be indispensable, where the groups that purvey conspiracy theories (and perhaps themselves formulate conspiracies) formulate their views through real-space informational networks rather than virtual networks. Infiltration of any kind poses well-known risks: perhaps agents will be asked to perform criminal acts to prove their bona fides, or (less plausibly) will themselves become persuaded by the conspiratorial views they are supposed to be undermining; perhaps agents will be unmasked and harmed by the infiltrated group. But the risks are generally greater for real-world infiltration, where the agent is exposed to more serious harms.
All these risk-reward tradeoffs deserve careful consideration. Particular tactics may or may not be cost-justified under particular circumstances. Our main suggestion is just that, whatever the tactical details, there would seem to be ample reason for government efforts to introduce some cognitive diversity into the groups that generate conspiracy theories. Social cascades are sometimes quite fragile, precisely because they are based on small slivers of information. Once corrective information is introduced, large numbers of people can be shifted to different views. If government is able to have credibility, or to act through credible agents, it might well be successful in dislodging beliefs that are held only because no one contradicts them. Likewise, polarization tends to decrease when divergent views are voiced within the group.69 Introducing a measure of cognitive diversity can break up the epistemological networks and clusters that supply conspiracy theories.
Conspiracy Theories, Cass Sunstein, pp 22-24






Additional Video Resources on Operation Trust
https://www.bitchute.com/video/ZBAZZpJ1vdjv
https://rumble.com/v1663ld-q-is-the-new-operation-trust-a-controlled-opposition.html